SECURITY PARTNERS
Supreme Security Collaboration
Inversion6 partners with the best and most secure innovators to protect you.
Some companies see cybersecurity as a cost center. We see things a little different. LEARN MORE >
Our seasoned Chief Information Security Officers bring strategic guidance to your leadership team, helping you right-size your cybersecurity operations.
A full suite of manage solutions from our US-based Security Operations Center (SOC)—staffed 24x7x365 by a full team of experienced analysts.
You can count on our IR team to contain the damage from a cyberattack, investigate the origins of the breach and build better protections for the future.
With an abundance of solutions and providers, the task of choosing the right option is critical and can sometimes be overwhelming.
Contact UsOur Continuous Monitoringsecurity operations center (SOC) identifies risks before they become problems.
We walk exactly as we talk.
Meet key regulations like SOC2, CMMC, PCI, ISO, 27001, HIPAA and others.
Get top-tier security experts without full-time staff costs.
Benefit from best practices across multiple sectors.
Scalable services to fit your business size and needs.
Our Continuous Monitoringsecurity operations center (SOC) identifies risks before they become problems.
We walk exactly as we talk.
Meet key regulations like SOC2, CMMC, PCI, ISO, 27001, HIPAA and others.
Get top-tier security experts without full-time staff costs.
Benefit from best practices across multiple sectors.
Scalable services to fit your business size and needs.

Inversion6 partners with the best and most secure innovators to protect you.

Inversion6 partners with the best and most secure innovators to protect you.
Inversion6’s TPRM provides continuous monitoring, risk assessment and mitigation strategies to ensure your business remains secure and compliant with the increased use of third parties.

Inversion6’s TPRM provides continuous monitoring, risk assessment and mitigation strategies to ensure your business remains secure and compliant with the increased use of third parties.



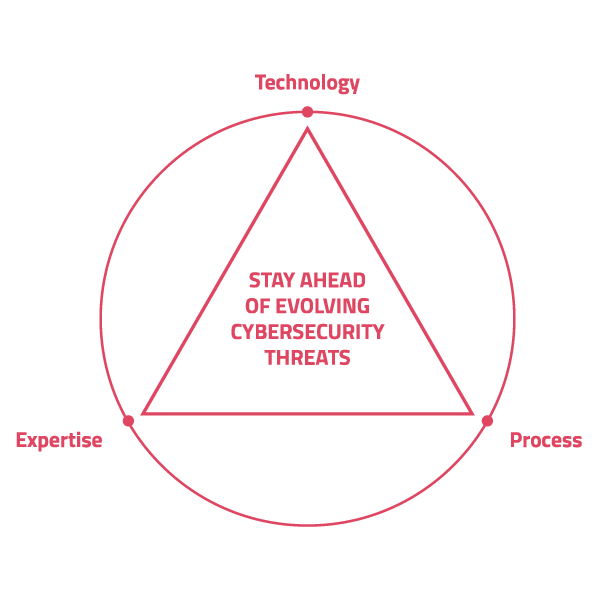
We take pride in our cybersecurity solutions
BENEFITS OF INVERSION6'S SECURITY PARTNERS:
Advanced threat protection against the latest cyber threats and attacks
Expert knowledge and experience of top tools for effective security strategies
Proactive monitoring to reduce risk and minimize potential damage



TECHNOLOGY PARTNERS
We don't push proprietary solutions. Instead, we carefully select the best technology partners to fit your unique cybersecurity needs. This approach ensures that you receive cutting-edge, reliable protection without any compromises.
TECHNOLOGY PARTNERS
We don't push proprietary solutions. Instead, we carefully select the best technology partners to fit your unique cybersecurity needs. This approach ensures that you receive cutting-edge, reliable protection without any compromises.



Mobile devices are increasingly targeted by cyber threats. What are you going to do?

Mobile devices are increasingly targeted by cyber threats. What are you going to do?

THE BENEFITS
We've mastered Microsoft security.
All so you can benefit from our experience and expertise. We provide real-time event correlation using both open-source and closed-source threat intelligence, expert configuration assistance, and the ability to automatically isolate and un-isolate infected systems.
What you get:
THE BENEFITS
We've mastered Microsoft security.
All so you can benefit from our experience and expertise. We provide real-time event correlation using both open-source and closed-source threat intelligence, expert configuration assistance, and the ability to automatically isolate and un-isolate infected systems.
What you get:

HTML stands for HyperText Markup Language. HTML is the standard markup language for describing the structure of web pages. Learn more.
HTML stands for HyperText Markup Language. HTML is the standard markup language for describing the structure of web pages. Learn more.
HTML stands for HyperText Markup Language. HTML is the standard markup language for describing the structure of web pages. Learn more.
HTML stands for HyperText Markup Language. HTML is the standard markup language for describing the structure of web pages. Learn more.
HTML stands for HyperText Markup Language. HTML is the standard markup language for describing the structure of web pages. Learn more.
HTML stands for HyperText Markup Language. HTML is the standard markup language for describing the structure of web pages. Learn more.
HTML stands for HyperText Markup Language. HTML is the standard markup language for describing the structure of web pages. Learn more.